Reporting¶
Reporting and logging is an extremely important part of running a Red Team engagement and PoshC2 ensures that every detail is logged to the database. It is always worth noting that PoshC2’s time-zone will work off the local server time, so if you are working in multiple countries or another time-zone, it is highly recommended that your time-zone is configured accordingly.
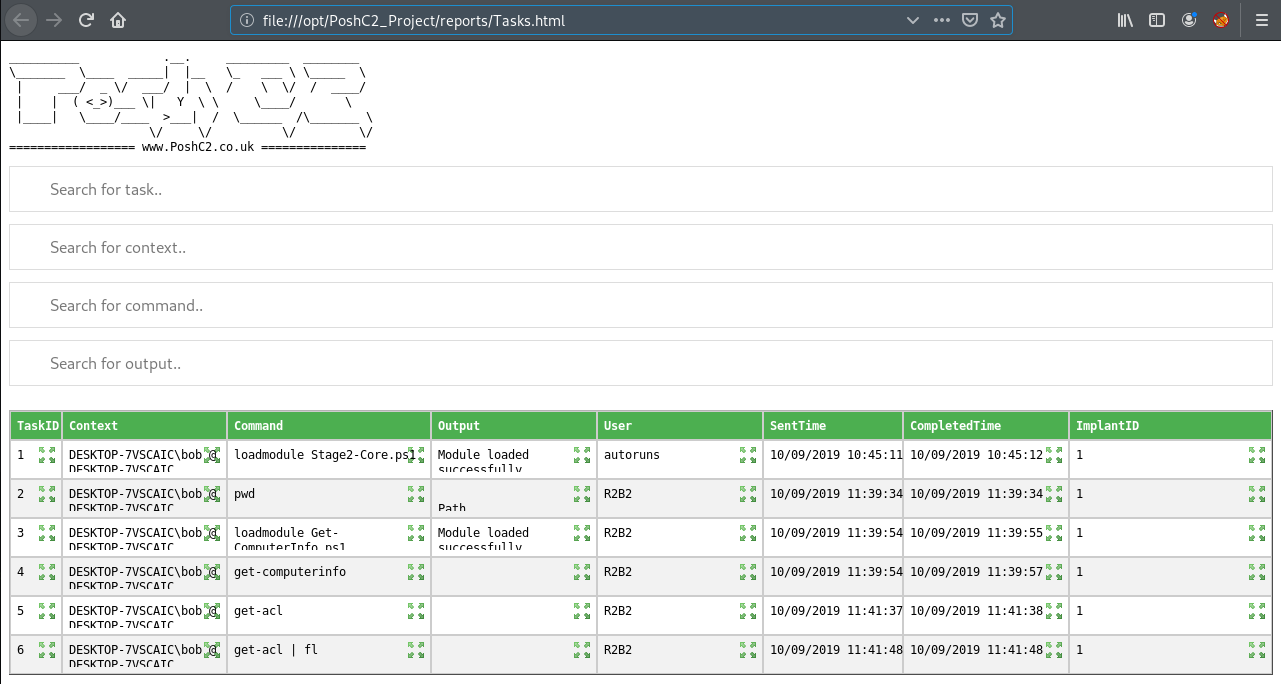
By default, PoshC2 records every command and all output from each Implant that is used and logs this information to the database, in addition to all the metadata around that command, such as the issuing user, the hostname and so on.
While the database can be interacted with directly, PoshC2 also has a number of reporting commands to aid in the processing of this information.
To output basic HTML reports from Implant-Handler top level prompt run the generate-reports command, which will generate a number of HTML pages to the reports directory in addition to dumping the data as CSV files.
The CSV files only can be generated using the generate-csvs command.
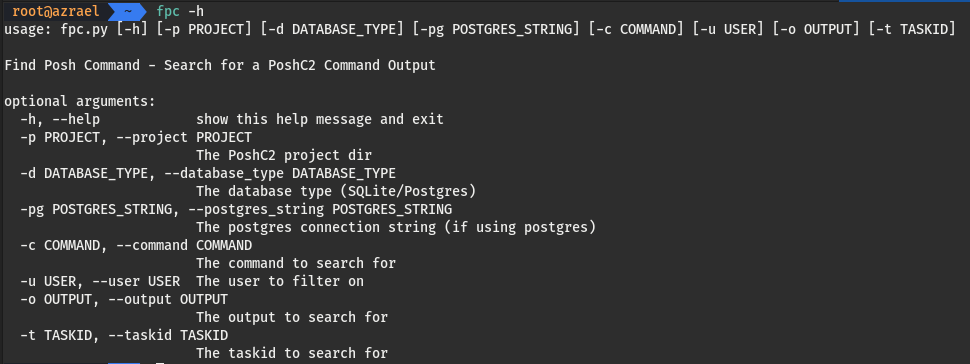
There is also the fpc command which can be used to find a PoshC2 command. This command can search through command input and output for search terms, and filter commands using a variety of filters.